Cost of Data breaches in India
India is no longer immune to security attacks and breaches. Internet has become the backbone of doing business. Indian companies are becoming easy target to attackers as a race to connect globally leaves them with gaping holes in their security implementation. Some companies with alleged breaches were Zomato, IndiGo Airlines, Cosmos Bank, JNU port, Jio and State Bank of Mauritius. Many breaches go unreported as companies feel revealing such information would impact their brand and that there is still no penalities on hiding breaches within an organisation. It has also been reported that 22,000 Indian websites were attacked between April 2017 to January 2018 alone. Indian businesses were top victims of ransomware attacks where 67% were hit with it. 9 in 10 companies who claim to have end point protection were attacked.
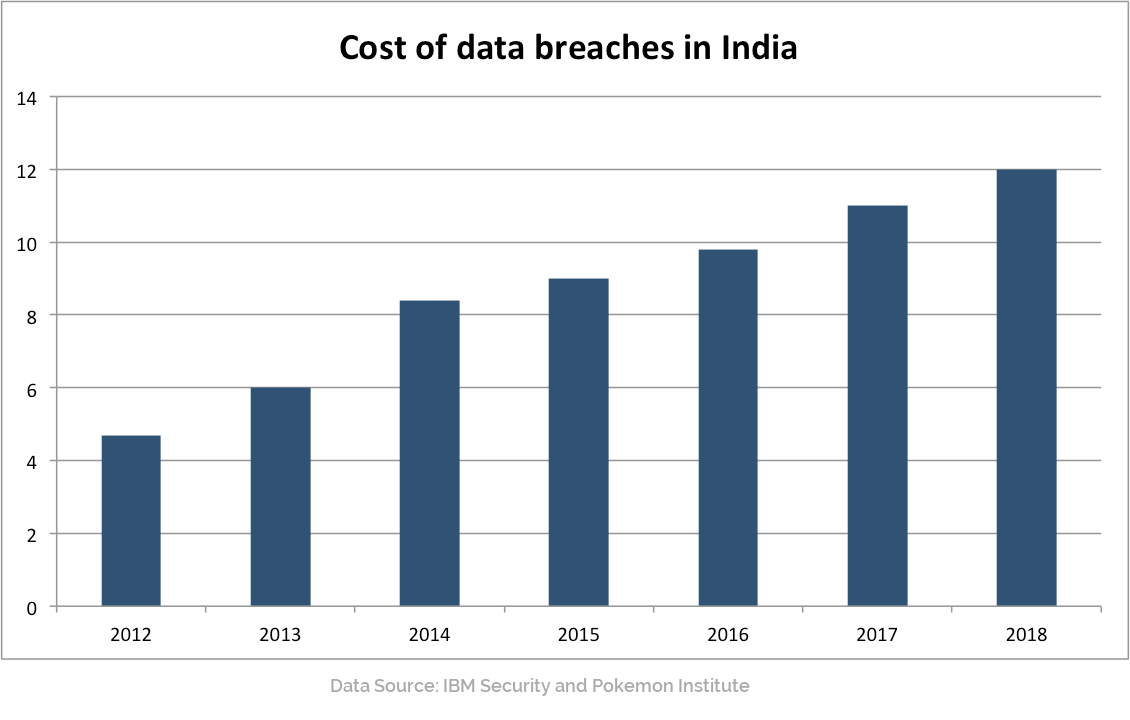
In the last five years, cost of data breaches in India have doubled and mind you this only takes into consideration of breaches which were reported. Government is working on a data privacy policy which will mandate all companies to report such breaches and they will be penalised too. Security is a serious business and it does not imply just installing a firewall or an end-point solution. According to Gartner, attackers use know vulnerability that remain unpatched as developing a new malware is far more expensive. By not patching servers or end-points and using outdated perimeter security, companies are left open to targets and there is very little cost for attackers in doing so.
Email are the easiest target to attack as organisations attackers get access to employees who are most vulnerable. Often mails are crafted to raise the curosity of an employee, like sending a ‘PO’ to a sales person, or sending a resume to an hr manager. As India moves rapidly to connect their businesses and use the internet as a platform to do commerce, managers need to understand that security has to become the core focus in their business architecture. Leaving gaps will not only lead to business losses, but allow reputation. Understanding various data contact points and ways to secure access from such points, will go a long way to improve security. Also, data needs to be encrypted so that even when an attackers has breached your gates, your company and consumer data is well protected.
Enterprises have also increased the use of SaaS applications. This leaves them exposed to data leaks as most perimeter security are unable to provide visibility of data that flows through such applications. Context based firewalls are able to watch the flows to SaaS applications and bring context to the information flowing to it, which leads to improved security by allowing organisation to treat SaaS applications like any layer 7 protocol and set policies based on such protocols.
Get In Touch With Us
Subscribe to our Newsletter
2025 © GajShield Infotech (I) Pvt. Ltd. All rights reserved.
