
The attack surface, also known by some as the attack surface area, is the digital part of an organisation that is the most vulnerable to hacking and other hostile cyber threats. If a cybercriminal somehow gets access into the data network or database of an organisation, they can increase this surface area.
Organisations value the protection and privacy of their data and control who has access to it. They certainly do not want their sensitive information to be privy to cyber criminals or their competition. If an organisation's security system is weak, it makes the hacker's task to extract all confidential information very easy.
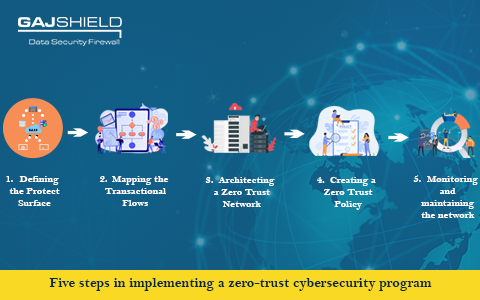
Zero Trust is a cyber security model which considers any request, whether it is within or outside an organisation, as a potential breach. It requires every request to be verified, encrypted and authorised before granting access. The execution of this program combines advanced technologies such as identity protection, risk-based multi-factor authentication, and robust cloud technology to verify or authenticate a system or user and then considers access as per the request.

The COVID-19 Pandemic has brought unprecedented changes into the lives of working people. A study revealed that about 82% of respondents accepted that they like to work from home rather than working at the office. The trend of working remotely, which was once enforced on the employees due to the pandemic, has become a new and preferred method of working.
Get In Touch With Us
Subscribe to our Newsletter
2025 © GajShield Infotech (I) Pvt. Ltd. All rights reserved.
