
Stop Malware at the Gateway, Before It Reaches Your Users
GajAV is the integrated antivirus module inside GajShield's Data Security Firewall. Every file crossing your network — downloaded from the web, received over email, uploaded to a portal — is inspected in real time and blocked the moment a threat is identified.
|
26+
File types inspected
|
16
Levels of nested archive inspection
|
Cloud
Reputation check & sandbox
|
24×7
Threat intelligence updates
|
| ▣ | Inline blocking — no user action required Infected files are stopped inside the firewall security stack. Users simply never receive them — there is nothing to click, nothing to clean up, and nothing to quarantine at the endpoint. |
From File to Verdict
GajAV operates as an integrated component of the GajShield firewall. Every file entering or leaving your network is inspected before it reaches the user or the server.
|
1
File Held at the GatewayFiles transferred over web, email, and file-sharing protocols are intercepted by the firewall and unpacked — archives, email attachments, documents, PDFs. Nothing moves forward until a verdict is returned. |
2
Inspected on the ApplianceEvery file and every extracted component is checked against GajShield's threat signature database and behavioural detection rules — in a single, fast inspection pass right on your firewall. |
3
Checked in the CloudUnfamiliar files are queried against GajShield's cloud reputation service and, when needed, safely opened inside a secure cloud sandbox to observe real behaviour — catching threats that have never been seen before. |
4
Blocked or DeliveredMalicious files are dropped at the firewall and an alert is logged. Clean files continue to the user untouched — with no delay that the end user can perceive. |
What GajAV Actually Does
Every capability below is already built into your GajShield firewall — working together in the same inspection pass, with no separate product to install or manage.
|
AV
Known Malware DetectionGajAV blocks known threats using a continuously updated signature database. Every file is fingerprinted and checked against millions of known malware samples — from classic viruses to the latest ransomware and trojans. |
ZIP
Deep Archive InspectionGajAV unpacks ZIP, RAR, 7-Zip, TAR, and other archives — up to sixteen levels deep — and scans every file inside. Attackers cannot bypass protection by hiding malware inside nested archives. |
@
Email Attachment ScanningInbound email is opened at the gateway. Every attachment, including files hidden inside encoded mail bodies and Unix mailbox formats, is extracted and scanned before the message reaches the user's inbox. |
|
DOC
Office Document InspectionWord, Excel, and PowerPoint files — both legacy and modern formats — are opened and their internal contents inspected. Malicious payloads hidden inside document streams are caught before delivery. |
PDF
PDF Threat AnalysisPDFs are opened and their embedded content extracted. GajAV flags documents containing suspicious scripts, automatic actions, and keyword patterns associated with PDF-borne attacks. |
EXE
Cross-Platform Executable DetectionWindows, Linux, and macOS executables are all identified and inspected. Protection extends beyond the Windows desktop to mixed environments, servers, and mobile application files. |
|
◊
Behavioural Threat DetectionAlongside signature matching, GajAV applies behavioural rules that recognise malicious patterns even in threats that have never been seen before — catching variants before signatures are published. |
APK
Mobile Application ScanningAndroid APK files downloaded over the network are unpacked and inspected for known mobile malware families — protecting BYOD users and corporate mobile fleets. |
↺
Live Signature UpdatesNew threat signatures are delivered continuously from GajShield's threat intelligence feed and applied to live traffic instantly — without interrupting any user or restarting any service. |
|
☁
Cloud Reputation CheckEvery file is checked against GajShield's cloud reputation service, drawing on intelligence gathered from the entire GajShield customer base. Threats seen anywhere in the network are blocked everywhere. |
⚙
Cloud Sandbox AnalysisUnknown and suspicious files are safely opened inside GajShield's secure cloud sandbox. Their real behaviour is observed — catching brand-new threats and never-before-seen malware that signatures alone would miss. |
☉
Zero-Day Threat ProtectionCombining cloud reputation with sandbox analysis, GajAV identifies and blocks zero-hour attacks — threats released in the last hours or days, before signature updates have reached any vendor. |
Every Common File Format, Inspected
GajAV recognises the file types your users actually work with — not just by file extension, but by inspecting the true content. Renaming a malicious file does not bypass protection.
|
Executables
Windows EXE and DLL files, Linux binaries, macOS applications, and Java programs.
|
Archives
ZIP, RAR, 7-Zip, TAR, GZIP, BZIP2, XZ, CAB, ISO disk images, and DMG macOS images.
|
|
Office Documents
Word, Excel, and PowerPoint — legacy (.doc, .xls, .ppt) and modern (.docx, .xlsx, .pptx) formats, plus RTF.
|
PDF Files
Including compressed internal streams, embedded JavaScript, automatic-action triggers, and suspicious keyword scoring.
|
|
Email Formats
Standard email messages, Unix mailbox archives, and encoded attachments in Base64 or Quoted-Printable form.
|
Mobile & Web
Android APK packages, Java JAR files, HTML pages, Flash SWF files, and active-content scripts (JavaScript, VBScript, PowerShell, batch).
|
Layered Protection in a Single Pass
GajAV combines multiple detection techniques — every file receives all of them, without the user or administrator having to choose, schedule, or configure anything.
|
|
||||
|
|
||||
|
|
||||
|
|
Threats Blocked Across Every Channel
Because GajAV sits inside the GajShield firewall, it inspects files no matter how they arrive. One module, every entry point.
|
WEB
Web DownloadsFiles downloaded over HTTP and HTTPS — from browsers, software updaters, and web applications — are inspected before they reach the user's device. |
MAIL
Email TrafficInbound and outbound email passing through the firewall is parsed, attachments are extracted, and every file is scanned before delivery. |
FILE
File TransfersFiles transferred over FTP and other file-sharing protocols are held, inspected, and released only after a clean verdict is returned. |
Part of the GajShield security stack. GajAV works alongside GajShield's intrusion prevention, URL filtering, application control, and data leak prevention engines — delivering defence in depth from a single appliance, with a single management console.
Built in India. Securing India.
GajAV is designed, developed, and maintained entirely in India by GajShield's engineering team. Reputation lookups and sandbox analysis run on GajShield's own Indian infrastructure — your intelligence never leaves Indian soil.
|
|
|
Ready to Block Malware at the Gateway?
Talk to a GajShield security expert. We will walk through GajAV's capabilities on your GajShield firewall, review your current environment, and demonstrate how threats are stopped before they reach a single user.
Multi-Wan Management
Control & Distribute Traffic Across Multiple Internet Links
Internet connectivity is at the heart of your business. Many businesses have multiple Internet connectivity (multi wan). Enterprises rely on the Internet to run their mission-critical business applications which drive their productivity and profits. It is expected that Internet connectivity to be highly reliable and always available. If the physical connection or the ISP goes down, organisations vital link to the Internet also goes down which affects business.
Revenue, customer satisfaction, partner relationships and employee productivity, all are at stake when internet link goes down. Internet outages impact an organisations email, websites, applications or VPN traffic.
GajShield’s ISP Failover & Load Balancing allows enterprises to control and distribute traffic across multiple internet links.
GajShield policy-based Failover & Load Balancing enables enterprises to distribute important applications over more robust internet links and less important applications over broadband connections as well as provide redundancy in case one more internet links are down.
Multi-Wan - ISP Link Redundancy – Failover
GajShield Multi wan or ISP Failover manages the traffic while providing valuable failover capabilities. That way if an internet link fails, GajShield senses the disturbance and redirects traffic to one of the working internet links.
GajShield checks the health of the available internet connections, continuously checks the status of all the internet links, detecting failures in real-time and automatically redirects the traffic to the operational internet links to guarantee full availability.
Customer can choose a granular option to define the primary internet link and multiple secondary internet links for each different service. For example for email the primary link could be ISP1, the secondary could be ISP2 and third link could be ISP3, while for FTP the primary could be ISP2, the secondary could ISP3 and third, could be ISP1.
Multi-Wan - ISP Load Balancing
GajShield Multi wan or ISP Load Balancing weighted round-robin method and hence it distributes the traffic across multiple internet links and provides the flexibility of utilizing the total bandwidth of all the internet links preventing bandwidth bottlenecks while minimizing the cost of inefficient bandwidth utilization. At the same time, GajShield detects any failure of the internet link and dynamically load balances the traffic over the available or Live internet link.
Integrated reporting and Alerts
GajShield reporting provides current, daily, monthly and yearly reports and trend analysis of ISP utilization, what applications are being used through the ISP’s and which user is using the ISP. Enterprises can determine misuse or abuse of internet links by applications and users to effectively utilize the internet links available and to make informed decisions related to bandwidth purchase and management. GajShield Alerting mechanism sends email alerts to administrators keeping them informed on the link outages facilitating rapid troubleshooting.
Features of GajShield Multi-Wan Management:
• Service-based ISP load balancing or failover.
• Both Failover and Load Balancing can be set up simultaneously.
• Load balances traffic based on weighted round-robin distribution.
• ISP Failover automatically shifts traffic from a failed link to a working link.
• Automatic traffic tailback when failed ISP comes. up
• Zone-based failover.
• Customized NAT on failover.
• ISP failover and tailback notifications on email.
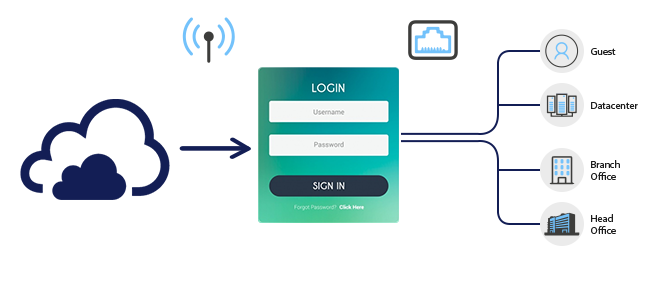
Secured Guest Management
A Solution to Monitoring and Control Network & Internet use by Guests
Guest visitors to an enterprise, hotel, colleges or even public hotspots might need access to the internet during their stay. The challenge faced by IT Managers is how to control and limit internet access of guest users without having to configure the guest’s desktop and yet have a solution which is cost-effective and easy to manage. IT Managers would need a solution which would provide a positive visitor experience without compromising the security of an enterprise.
In providing internet access which could be for a day or even weeks during the stay of a guest, another challenge IT Managers face is creating temporary user IDs for guests. Maintaining such a large changing list of users is a tedious job for an admin. It is also difficult to apply access restrictions to these users, as users database is frequently changing/getting updated.
Solution
GajShield’s SECURE GUEST INTERNET MANAGEMENT SYSTEM fulfils all the above requirements, yet it is simple to manage, scalable and cost-effective too. The system helps to manage guest users, whether wired, wireless or even using mobile for internet access. Its auto expiry feature makes it easy to manage large sets of guest users. Its reporting system gives in-depth usage information and helps to identify any misuse by these users.
With this system, the IT Administrator can create guest users manually or provide an option to guests for self-registration. GajShield's Data Security Firewall provides user credentials via SMS which expires after a pre-configured / pre-defined time. Security policies can either be set for the guest group or can be defined for an individual user.
By terminating the guest network on a separate port of GajShield Firewall, enterprises can also control and limit guest users access to a corporate network.
Prerequisites
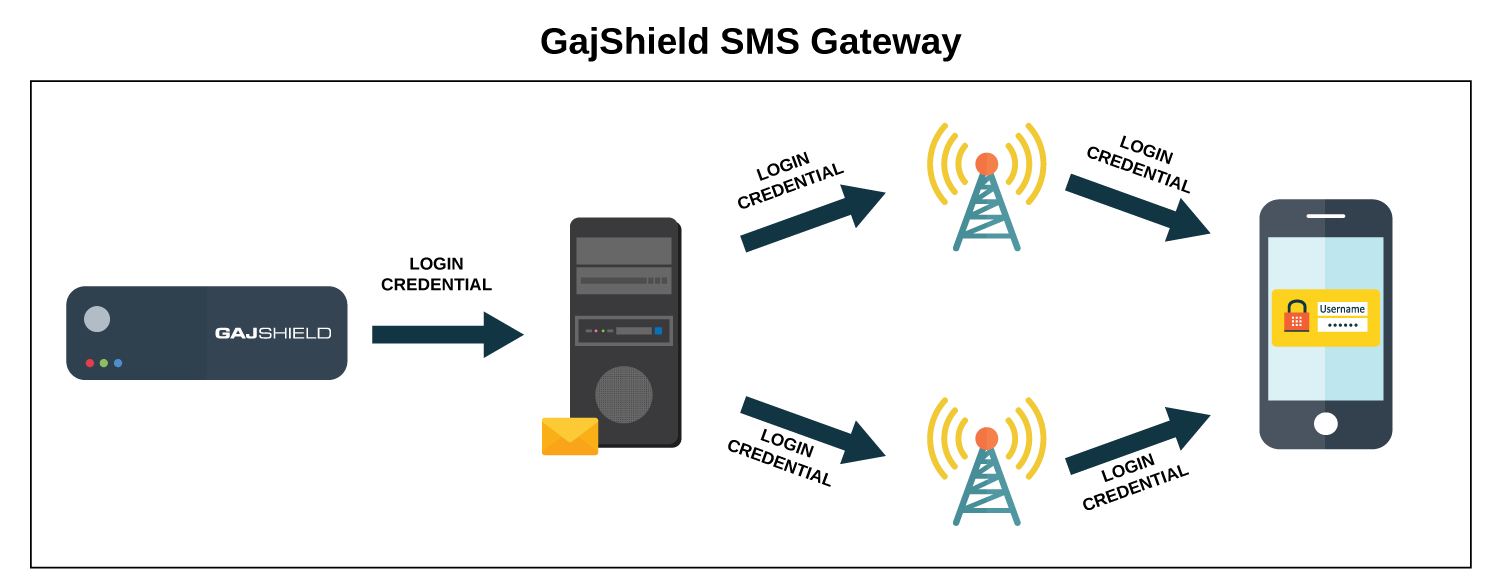
SMS Gateway
User credentials can be either sent via email or using SMS. To send Username and Password via SMS, the organisation will have to be registered with an SMS Gateway service provider. GajShield Firewalls come with pre-configured API parameters for various service providers. For service providers not listed in GajShield, the API parameters would have to be obtained and configured on GajShield Firewalls.
Features:
GajShield Guest Management System simplifies administration of guest users, a tremendous benefit for IT staff that will have a very limited workload in the daily operation.
Guest login portal
This is the interface used by guests and gives the very important first impression of a company. This portal is customized according to the organization and is a powerful branding as well as an information delivery tool. Guests connecting their laptop or smartphone to the internet will immediately be redirected to this portal. They will then log in to access the Internet.
One of the more popular guest provisionings flows is guest self-registration with SMS activation:
- The guest registers and enters his/her mobile number at the guest login portal.
- A one-time access code/ username and password is delivered to the mobile phone via SMS (Short Message Service).
- The guest activates the guest account using a provided username and password.
The use of activation through the mobile number enables traceability of the guest’s activity in the network as the identity of the guest will be automatically validated through the mobile subscription.
Guest Administration
This works as a control centre for IT staff. The Firewall Management System helps in configuring security policies for guest users along with configuring SMS gateway, guest portal and registration. It also provides a detailed reporting system built with intelligence to identify anomalies and misuse of policies.
Along with the above features, GajShield solution also provides:
- Create Guest Users Manually or User can register themselves through the Registration process
- Add Guest Users in bulk (through CSV upload)
- Delete Multiple Guest Users manually or enable Auto-Delete (automatically deletes user on expiry of validity)
- View Guest User Registration and Auto-Delete Logs
- Option to resend Guest User Credentials on SMS
- Create Group(s) of Guest Users
- Apply Security Policies (like URL, DLP, Application Filter Policies) based on Guest User(s) and/or Group(s) of Guest Users
- Apply Bandwidth Capping/Queue on Guest User(s) and/or Group(s) of Guest Users
- Apply UserSense Sessions and Authentication Schedule (Time Schedule) based on Guest User(s) and/or Group(s) of Guest Users
- Apply Bandwidth and/or Time Quota on Guest User(s) and/or Group(s) of Guest Users
- Can route traffic of Guest User(s)/ Group(s) of Guest Users through different ISP(s)
- Can apply BYOD restriction on Guest User(s) and/or Group(s) of Guest Users
SD-Wan
A Modern Networking Solution for the Digital World
The speed of business continues to accelerate. Competition is fiercer than ever; customer expectations are higher than ever. Today’s businesses run on applications and rely on connectivity, and when you’re opening up new sites or branches, time is money.
Geographically distributed organizations often have hundreds or even thousands of branch offices connected to a hub or headquarters’ sites. For security reasons, cloud-based application traffic is often backhauled from the branch across expensive WAN/MPLS links to a hub site before being handed off to the Internet. Not only is this expensive, but performance is often compromised due to WAN bandwidth constraints at the branch and added latency from backhauling connections.
A solution is to use direct Internet connection that provides simpler and consistent performance to cloud-based applications. With GajShield Data Security Firewalls, Internet connections become secure and reliable, it helps in augmenting or even replacing the traditional MPLS connections and lower WAN costs.
GajShield GS-Branch:
Distributed enterprise branches transitioning to a digital business model have a significant impact on their network. With enterprise users both remote and local directly accessing the internet for cloud and Security-as-a-Service (SaaS) applications, the WAN and access edges are getting more complicated than ever and introduce new vulnerabilities for attackers to exploit. GajShield Firewalls enables customers to converge their security and network access, extending the benefits to their distributed branches. GajShield security device is comprised of GajShield Data Security Firewall, Secure Access using VPN, Anti Malware with Advance Threat Protection to deliver consolidation of branch services for network edge and device edge protection.
Features:
- Centralised policy management
- Easy operations with minimum learning curve
- Flexible deployment
- Consolidated Network and threat visibility
- Allows grouping of security appliances
- Complete threat protection including firewall, gateway anti malware, DLP, application control, intrusion prevention system and URL filtering
- Re-usable policy templates.
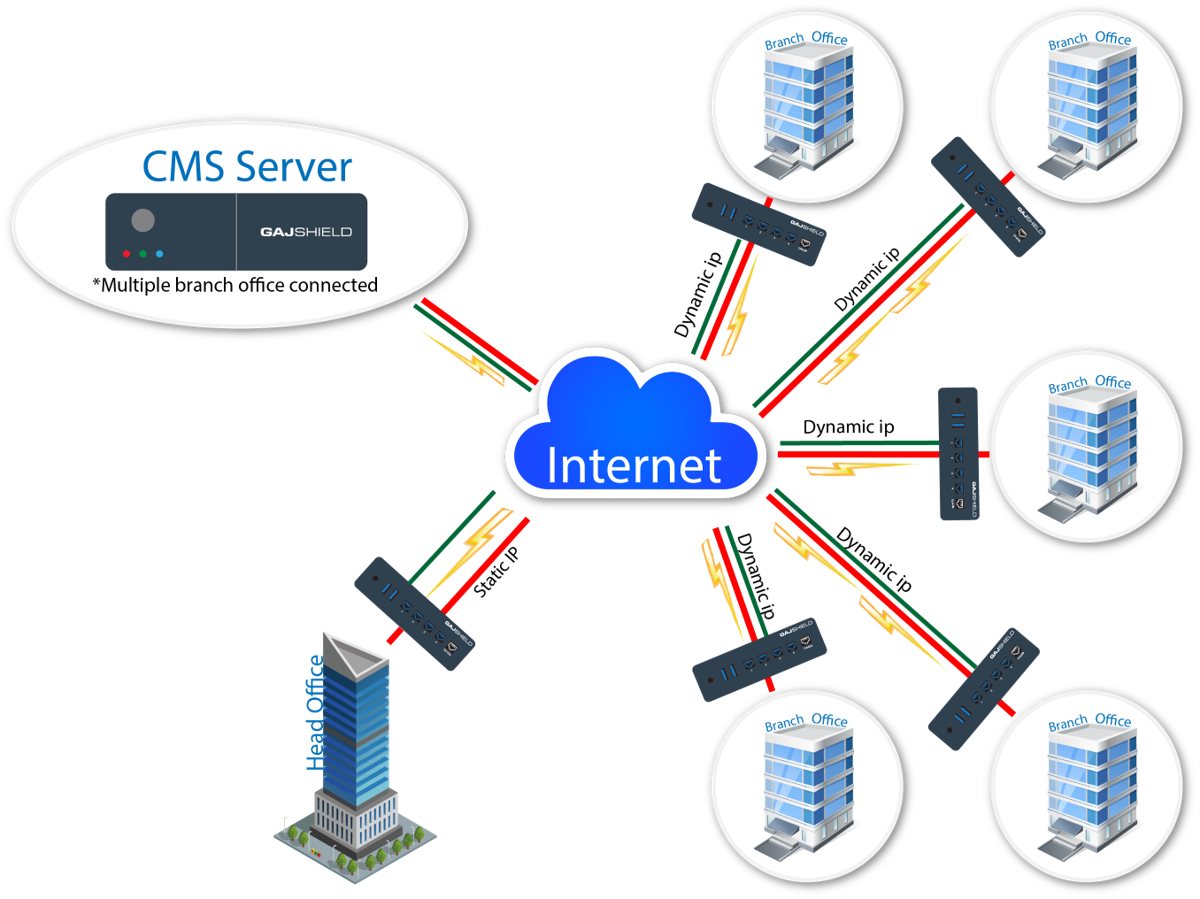
Centralized Management System
Quick Deployment:
GajShield’s simplified and easy deployment capabilities allow enterprises to ship unconfigured GajShield Data Security Firewall appliances to each remote site. When plugged in, the appliance automatically connects to the service in Centralized Management Service Server. Within seconds, the server authenticates the remote device and connects it to a Central Management System. The GajShield Centralised Management System is a dedicated network security management appliance, that enables network admin to manage distributed network of GajShield Firewalls, like managing all aspects of device configuration, push global policies, view all firewall traffic, and generate reports — all from one central location using a single console. Multi-path technology can automatically failover to the best available link when the primary WAN path degrades. This automation is built into the GajShield’s Multi-WAN management, which reduces complexity for end-users while improving their experience and productivity.
Benefits
- Lower Cost or Setup and Operation
With the help of Centralised GajShield Security Management Architecture, enterprises can deploy and manage multiple Internet links, you can now augment or even replace MPLS connections with broadband internet services to connect users to applications and lower WAN costs by up to 90%. The ROI is dramatic and immediate.
- Better Performance
GajShield Security Architecture is powered by multi-core architecture which provides faster application steering and unrivalled application identification performance. This includes deep secure sockets layer (SSL)/transport layer security (TLS) inspection with the lowest possible performance degradation.
GajShield’s MultiWAN management helps in routing applications and users over the most efficient WAN connection at any point in time. To ensure optimal application performance, it identifies a broad range of applications and applies routing policies at a very granular level for better end-user productivity.
GajShield’s application engine uses an application control database with the signatures to identify various applications (plus regular updates from GajShield threat Lab). GajShield identifies and classifies applications, even encrypted cloud application traffic, from the very first packet. This can be set to recognize applications by business criticality. Unique policies can be applied at a deeper level for sub-applications. This deep and broad application-level visibility into traffic patterns and utilization offers a better position to allocate WAN resources according to business needs. - Highly Available
One of the goals of high availability is to eliminate single points of failure in your infrastructure. A single point of failure is a component of your technology stack that would cause a service interruption if it became unavailable. As such, any component that is a requisite for the proper functionality of your application that does not have redundancy is considered to be a single point of failure.
High availability is an important subset of reliability engineering, focused towards assuring that a system or component has a high level of operational performance in a given period of time. At the first glance, its implementation might seem quite complex; however, with GajShield it becomes much simpler and it can bring tremendous benefits for systems that require increased reliability.
Better Security
- Data Leak Prevention
DLP identifies, monitors and protects the data in motion on your network through deep content inspection and contextual security analysis of transactions, DLP systems act as enforcers of data security policies. They provide a centralized management framework designed to detect and prevent the unauthorized use and transmission of your confidential information. DLP protects against mistakes that lead to data leaks and intentional misuse by insiders, as well as external attacks on your information infrastructure.
- Contextual Intelligence Engine
Contextual Intelligence Engine is a technology that allows to gain advanced visibility of data transaction over applications that uses network. Context-based security approach is a step ahead from traditional firewall capabilities. Using deep inspection at Different Levels for advanced security, Contextual Intelligence Engine understands the application and its data context. It allows to create a context of Saas applications and understand its usage, much deeper than just the application. Combined with Machine Learning, the contextual intelligent engine helps in finding anomalies.
- Intelligent Sandboxing
An Intelligent Network Sandbox solution that has anti-evasion capability for protection against malware that understands and detects a virtual environment. With the ability to sandbox various file types and embedded URLs, our intelligent sandbox inspects content that a traditional signature-based antivirus cannot identify as malicious and categories accordingly.
- GajShield Threat Lab
Proactive virus detection, Robust and inherent immune system that integrates Zero-Hour (Zero-Day) Virus Outbreak Protection to shield enterprises in the earliest moments of malware outbreaks, and right through as new variants emerge. By proactively scanning the Internet and identifying massive virus outbreaks as soon as they emerge, proactive virus blocking is effective and signature independent. At the Threat Lab, a database of real-time spam outbreaks is collected and compiled and maintained, through consultation with global Internet Service Providers. Patterns are analyzed, categorized, and cross-matched using algorithms, run to optimize the detection of repeating patterns and their sources. This database, containing approximately over six million signatures, is continuously updated with more than 30,000 new unique signatures added hourly.
Gateway Anti-Malware
- Powerful and Real-Time protection from Virus outbreaks
- Scans HTTP, HTTPS, FTP, POP3, SMTP & SMTPS traffic
- Detects and removes viruses, worms and all kinds of malware
- Instant identification of virus-infected users
- ZERO Hour Virus protection
- Spyware, Malware, Phishing protection
- Automatic real-time Virus update
- Complete protection of traffic over all protocols
- Last virus update definition
- Complete report
Security-Driven Networking
GajShield enables best-of-breed software-driven networking that is both high-performance and protected. GajShield Data Security Firewall featuring multi-core architecture to deliver faster network management with extreme security performance. GajShield has robust threat protection, including Layer 3 through Layer 7 security controls and data-level visibility. Featuring Complete threat protection, including firewall, antivirus, intrusion prevention system (IPS), and application control High-throughput SSL inspection with minimal performance degradation, ensuring that organizations do not sacrifice throughput for complete threat protection against zero-day threat. Web filtering to enforce internet security and Highly scalable & throughput overlay VPN tunnels to ensure that confidential traffic is always encrypted.
Page 1 of 18

