GajShield SOLUTIONS
GajShield AdvantagesValue Proposition
GajShield Firewall solutions helps in keeping threats away from the organization right at the gateway level. We understand the cyber threat space and have created solutions that helps in securing the organization from threats that are often left unnoticed. We use the latest and the greatest of technologies like the Contextual Intelligence Engine©, Machine Learning etc. for an Intelligent Security Solutions combined with Advanced Deep Visibility for ultimate security.
Advantages of GajShield
- Data Understanding product & solutions:
Looking at the current cyber-attack trends and other security solutions, GajShield has worked towards developing a product that understand the Data for better security.
- Preventing Data Leaks
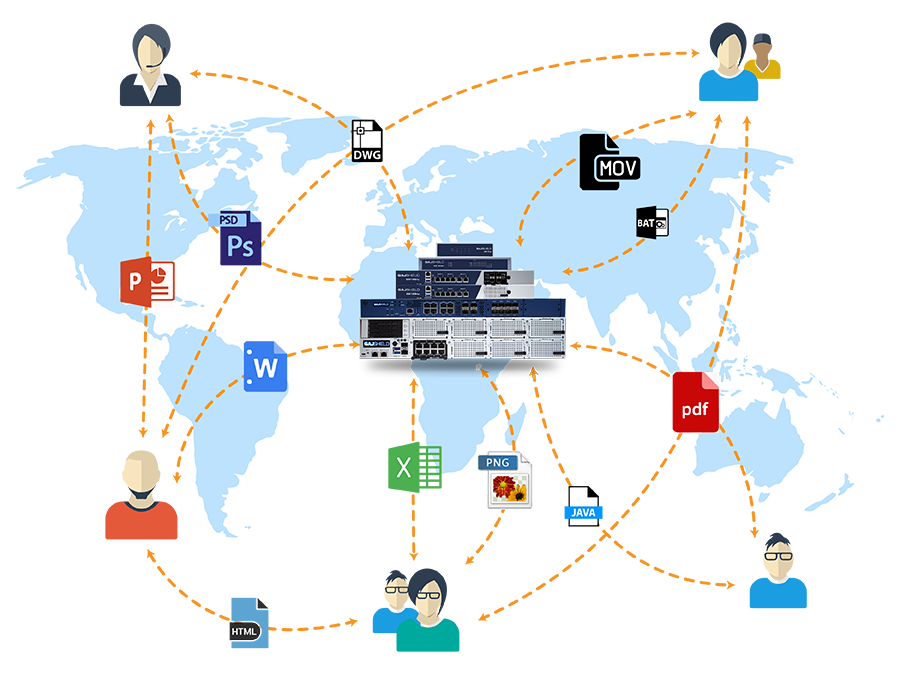
GajShield uses a Context Based Network Data Leak Prevention to prevent business critical data from being leaked out through various gateways like Email, SaaS application like Gmail, Google Drive, etc. and other popular social media platforms.
- Protection against Email Borne Threats
Email being the go-to means of business communication, attracts threats through it. GajShield uses Advanced Email Security Solution to protect from Email Borne malware, virus, business email compromise attacks and more.
- Protection from Threat
At GajShield, we understand various threat vectors and help organizations to protect from the commonly ignored intentional and unintentional threats using intelligent security solutions.
- Security for Roaming Users
Roaming users are the most accessible and easy targets for a lot of a?ackers. GajShield enforces roaming users to route all network traffic through the firewall at HO, bringing them under a secured network.
- Unified Platform for Security
GajShield’s constant research and development has led to the creating of a uniformed platform for both network and data security.
- Contextual Security
GajShield leverages its capability to provide visibility of data context, deeper than the traditional Layer 7 application visibility and performs proactive scanning to identify exactly which application, threat vector and user makes the network vulnerable and increases visibility, data security and performance.
Enterprise Cloud
A Solution to Secure Enterprises' Roaming Users
Roaming users are the most vulnerable entry point to any organizations and with remote working becoming an increasingly popular trend among workers, enterprises are feeling the need to implement strict policies to secure their valuable data. However, despite devising strict and detailed policies for the use of personal mobile devices, enterprise cybersecurity teams are often let down by solutions that fail to enforce their security policies across a variety of devices and networks (like public Wi-Fi hotspots). As a result, they are vulnerable to data leaks and cyber-attacks through the devices carried by their roaming users.
That’s why, to prevent data leaks and act as the threat vector, roaming users regardless of the device and network they use, GajShield’s Data Security Firewall with the help of Enterprise Cloud Solution, ensure that all users, roaming or otherwise, are secured when they access enterprise data and applications when they step out of the enterprise network. Even if they use public Wi-Fi networks, the cloud security solution scans every packet of data being transmitted by users with its Deep packet Inspection (DPI) capability combined with Contextual Intelligence Engine to create context of all the traffic for the Data Security Firewall to understand and take necessary action. As a result, if any communication to or from the roaming user contains sensitive data that shouldn’t leave the organization, the Data Security Firewall blocks such communications based on defined data security policies. It also identifies malware and suspicious files that can infect the enterprise applications and blocks them from running and causing harm to the enterprise network, saving from a cyber-attack.
GajShield’s Enterprise Cloud Solution enforces routing of all traffic through the HO’s Data Security Firewall (Public or Private) and applies all the data security and global security policies to all the browsing and network activity. This allows the organizations to gain complete visibility on all the network traffic of the roaming user for monitoring along with the greatest of security solutions to ensure maximum Security and prevent data leak.
GajShield allows organization to decrypt SSL traffic to detect and block hidden malicious content or outgoing sensitive information. GajShield inspects and protects the organization against known viruses and worms using signature and heuristic technologies. GajShield’s architecture provides inspection at many levels and at regular times with the speed of most competitive products, ensuring full protection without introducing latency. In addition to this, a range of spyware, including malicious Trojans, system monitors, key-loggers, and adware, which are pervasive threats and significant security risks, are effectively detected and stopped by GajShield’s antispyware. Security is ensured to the roaming users even when they are a part of an insecure network like public Wi-Fi, etc.
Besides this, GajShield allows that organization to decrypt SSL traffic to detect and block hidden malicious content or outgoing sensitive information.
As the traditional perimeter is vanishing with enterprises connecting to their customers and partners, data leakage and cyber-attacks are becoming an expensive, burdensome problem. Employees, whether their intent is innocent or malicious, can easily send a Webmail or IM with confidential information. Information can be posted on social networks and blogs instantaneously. Private information, such as consumer’s Social Security and Credit Card numbers are protected by Government regulations and leakage creates legal liabilities and harms brand reputation. Furthermore, leaks of sensitive company information may lead into financial losses.

Enterprise Cloud Functionality:
GajShield Data Security Firewall provides an integrated, best-of-breed, and comprehensive functionality. It allows organizations to create common, granular policies for various areas. It has an intuitive user interface, so that use of the service literally requires no training. There are three key areas of functionality: secure, manage, and comply GajShield inspects all outbound and inbound web traffic to protect enterprises from these threats.
- Enforcing of security policies and control including web filtering, application filtering, DLP along with visibility of roaming users (using cloud client).
- Restricts roaming users to disable security policies.
- Viruses, Malwares & Spyware: The Known Threats.
- GajShield inspects and protects against known viruses and worms using signature and heuristic technologies.
- GajShield’s architecture provides inspection at many times the speed of most competitive products, ensuring full protection without introducing latency. In addition, spyware is a pervasive and significant security risk. GajShield antispyware detects and stops a range of spyware, including malicious Trojans, system monitors, keyloggers, and adware.
- Web traffic is increasingly being encrypted using the SSL protocol. If an organization selects SSL decryption policy, GajShield allows that organization to decrypt SSL traffic to detect and block hidden malicious content or outgoing sensitive information.
- As the traditional perimeter is vanishing, with enterprises connecting to their customers and partners, data leakage is becoming an expensive, burdensome problem. Employees, whether their intent is innocent or malicious, can easily send a Webmail or IM with confidential information. Information can be posted on social networks and blogs instantaneously. Private information, such as consumers’ Social Security and credit card numbers, is protected by government regulations and leakage creates legal liabilities and harms brand reputation. Further, leaks of sensitive company information risk financial loss.
- Several companies have emerged to offer specialized solutions to prevent data leakage. These solutions often require extensive implementation and consulting services. They are also just another point solution to be added to an already-crowded perimeter gateway. Not surprisingly, less than 5% enterprises have deployed data loss prevention (DLP) solutions today.
- GajShield CASB (Cloud Access Security Broker) provides in depth security for well-known SaaS applications like Google G-Suite, Office 365, Yahoo, Rediff Mail, Facebook and others. Cloud Access Security Broker (CASB).
- GajShield DLP solution provide in depth visibility to the data which is sent out of your corporate asset
Benefits:
- No end point security product required, improves performance
- Mobile users comply to company policies even when they are not in the network
- Central policies with ease of management for mobile users
- High end infrastructure protecting cloud user
Further Reading
Case Study: Zodiac Clothing Company uses GajShield Cloud Security to secure its 130+ stores
Complete Visibility
Gain Deep Dive into Data Context of Application
It has been evident and have become a thumb rule for cybersecurity to have visibility on things we want to protect. Simply, you cannot protect that you cannot see. While Cybersecurity is never a static, one-time initiative but an ongoing process that should always be top-of-mind for CSOs, CIOs, and other IT leaders. To that end, technology and security leaders should always have access to information regarding the security of their enterprise networks possible only if they have visibility not only on their network but beyond just the network. In fact, not just the leaders but even employees need real-time Data visibility to report any damage to or illicit use of the organization’s Critical Data. And ensuring enterprise-wide Data visibility should be a priority even if the organization uses the most cutting-edge cybersecurity tools and technologies. That’s because cybersecurity systems, while generally being effective at keeping bad actors out and sensitive data in, cannot keep your Data protected all the time and from all threats if it does not have visibility. There can always emerge newer forms of threats that may require the immediate attention of an enterprise’s cybersecurity personnel and leaders. And the time it takes between a threat’s incipience and the cybersecurity team’s awareness of it can be the difference between security and enterprise-wide mayhem.
The most compelling reason as to why data visibility is a must for data security is simply that it is impossible to protect what you can’t see. An enterprise data must be monitored everytime it exists the organization. That means having real-time knowledge of:
- Every piece of information that is transmitted to, from, and within the organizational network.
- The source and destination (E.g. URLs, email IDs, body content, subject, attachments, content of attachments etc.) of every inbound and outbound communication.
- Gains visibility on internet activities of computer devices used by the enterprise, which includes all the laptop computer devices used by employees from other remote locations.
At GajShield we understand how enterprises workforce make use of data in their day to day activities and the importance of data for business continuity. These data are very useful and if fallen in wrong hands, can result into disastrous situations. To protect these data and prevent data exploitation, one must have visibility beyond just the traditional Layer 7 to understand i.e. understand of further contextual data that is associated with the identified application in use.
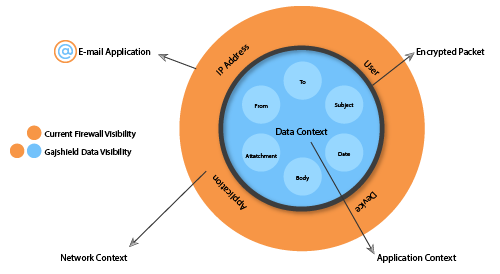
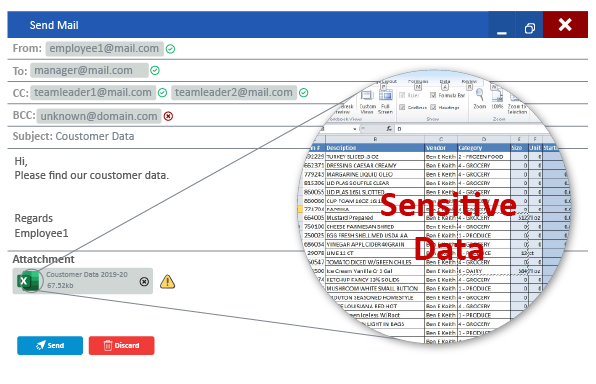
GajShield Data Security Firewall uses Contextual Intelligence Engine and Combines it with advanced reporting capabilities of GajOS: Bulwark for Enterprises to augment their traditional layer 3 (network level) security with a layer 7 (application level) security solutions and deep dive past than just the layer 7 into Data Context to create contextual information. GajShield Data Security Firewalls perform Data Layer inspection with the help of Contextual Intelligence Engine to create data context and analyze a broader range of parameters with greater in-depth data layer visibility, extending the visibility to more data like Email ID, Sender ID, recipient ID, CC mentions, Subject, Mail Body, Signature, File Content, downloader, uploader etc. across web traffic and SaaS applications to identify abnormal behaviors that may indicate potential cyber and data threats.
Analyzing these parameters, the Data Security Firewall determines the safety and legitimacy of communications & transactions and takes necessary actions to prevent data exploitation and this capability can is useful in mitigating the impact of a zero-day attacks.
Using GajOS Bulwark, GajShield Data Security Firewall provides
- Complete visibility of the applications and bandwidth used.
- Complete visibility of evasive applications like P2P and Skype application.
- Complete insight on :
- Content upload via Web uploads ex: webmail, Social networking sites, Blogs, Instant Messaging, Mail.
- Content sent through email.
- Content sent through Instant Messaging.
- Comprehensive reporting on :
- Top Internet Users.
- Top Bandwidth Users.
- User/Group Activity.
- Application Traffic.
- P2P Usage.
- URL/Category Usage.
- Total Internet Traffic.
- Application Traffic, Total Traffic, Application set and application detail.
- Web Browsing by URL, Category and User.
- Trend Analysis of applications, users and bandwidth.
- Current, Daily, Monthly, Yearly reports And much more.
Data Leak Prevention
A Unique Context-Based Network Data Leak Prevention
The Data Leak Prevention Solution is an integral part of the Data Security Firewall and acts as a core solution that helps prevent data leak through various platforms. The Data Leak Prevention Solution integrated within the Data Security Firewall identifies, monitors, logs and prevents misuse and exploitation of the data when transferred from your organizational network through deep content inspection and a contextual security analysis of transactions, DLP systems act as enforcers of data security policies. They provide a centralized management framework designed to detect and prevent the unauthorized use and transmission of your confidential information. DLP protects against mistakes that lead to data leaks and intentional misuse by insiders, as well as external attacks on your information infrastructure.
Features of GajShield Gateway DLP:
- Protect Business-Critical Data.
- Protects Data in Motion.
- Protect from Intentional and unintentional Data Leak.
- Prevent IT Shadow
- Agentless solution
Prevent Sensitive Data Leak
Advantages:
- Deep inspection of application data:
Deep dive a layer into applications by using deep inspection and contextual intelligence engine to create data context, beyond just the application contexts. For better, deeper information visibility and better security. It can prevent data leak based on contextual parameter on both application and data level like restricting ‘From’, ‘To’, ‘Subject’, ‘Email Data’, ‘Attachments’ etc. in email applications and other parameters for various other SaaS Applications.
- Control Data inflow and outflow:
Gain complete control over what goes and comes into your network. Now set policies to allow or block certain content to be sent out or downloaded of the network to control the inflow and outflow of the data.
- Context-sensitive data leak prevention
Using contextual intelligence, now you can define data leak prevention policies based on textual content inside the file. The DLP can block file based on textual content it carries. For example, If in an organization, keywords like “tenders”, “Quotation” are blocked, the users will be restricted to send emails or documents and attachments consisting of these keywords words. The Deep Packet Inspection inspects the file content attached to a mail, being uploaded to a file-sharing application, file sharing application, social media etc.
- Block Allow Data type, file extension, file content and more.
Explore the possibilities of blocking and allowing file type that can be downloaded or uploaded using the Data Leak Prevention solution that has the capability to identify the file type and its extension.
- Prevent Data Leak on SaaS Applications.
GajShield’s CASB (Cloud Access Security Broker) works on a proactive detection model to ensures that all the communication between the on-premise device and cloud application provider complies with the organization’s security policies. It uses information from the Contextual Intelligence Engine, check for compliance with Data Leak Prevention Policies to detect and take necessary action against an unsanctioned use.
- Control and Secured Entry Point for advanced security
A Roaming user, once out of the office environment is a major source for a data leak when not under the organization's network. Combining enterprise cloud, the organization can now enforce all communication to be routed through the HO firewall so as to protect from any intentional or unintentional data leak.
- Restrict Personal Use:
Now monitor and control the use of all non-business application and increase productivity. The Data Leak Prevention allows setting of policies to restrict the use of personal email and social media ID and allow only corporate logins. This looks beyond the traditional approach of blocking website and allows the use of useful applications and social media while controlling the use of it with complete visibility.
UPLOAD LOGS
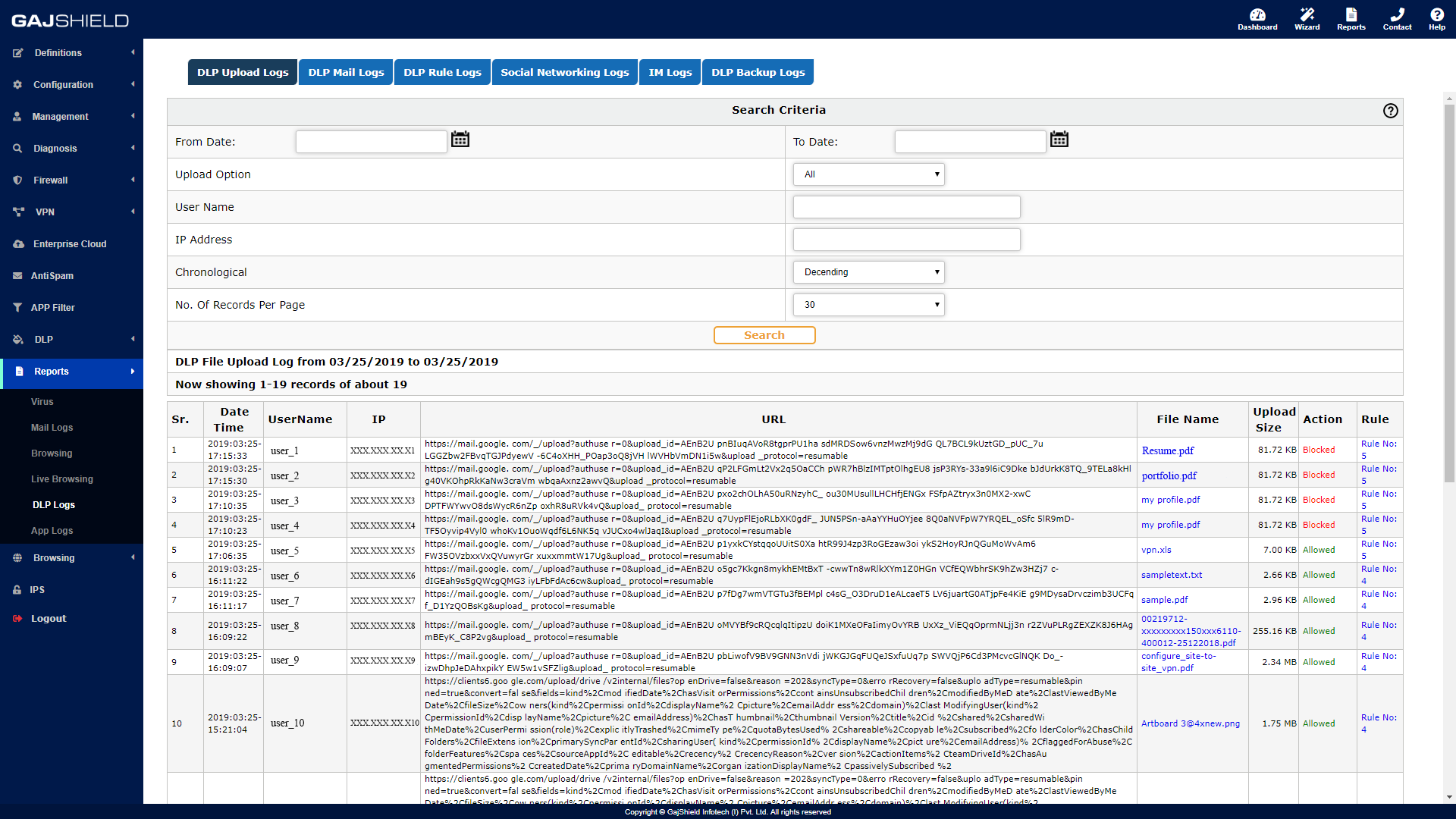
MAIL LOGS
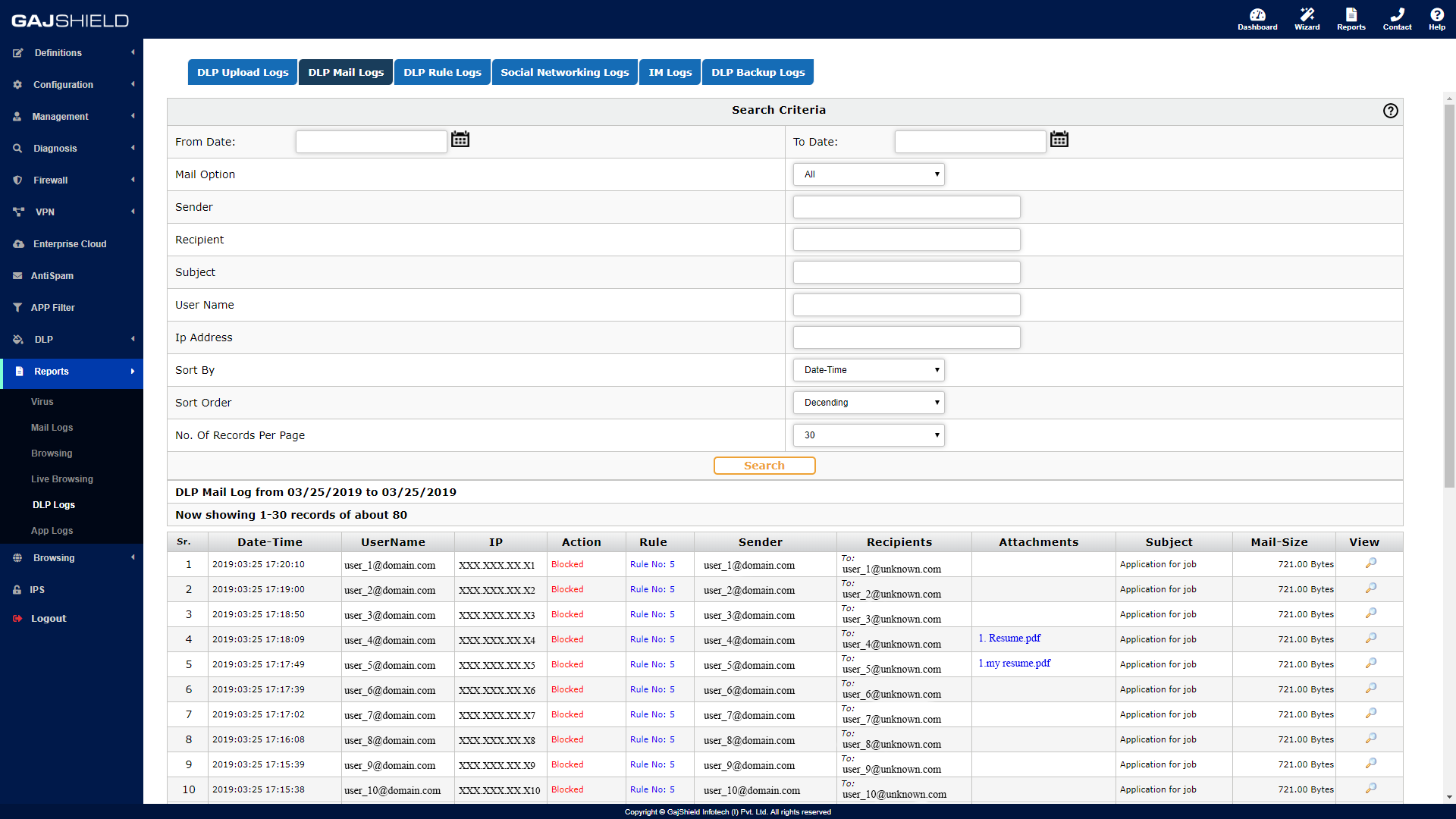
SOCIAL MEDIA LOGS
Why is Data Leak a Concern? This is what customers are telling us about Data Leaks.
- Loss of Sensitive Information - "I don’t know how we can control data from being sent in email or uploaded to the Web."
- Inadvertent Misuse - “Most of our policy violations and information breaches are accidental!"
- Collaboration Risk - "I think some of my employees are posting and sharing confidential information on Social Networking Site like Facebook."
- Context-Sensitive - “My current Data Leak Prevention System causes a lot of false-positive and block data as it is unable to understand the Web application.”
- In-depth Visibility - "Need in-depth visibility on the sensitive data that my employees are uploading. Would be wonderful, if it could give this information in a readable format."
- Data Leak outside Network Perimeter - "What happens when my employees carry their laptop while travelling. Need to control and prevent leaks even when they are out of office.”
Data Leak Statistics
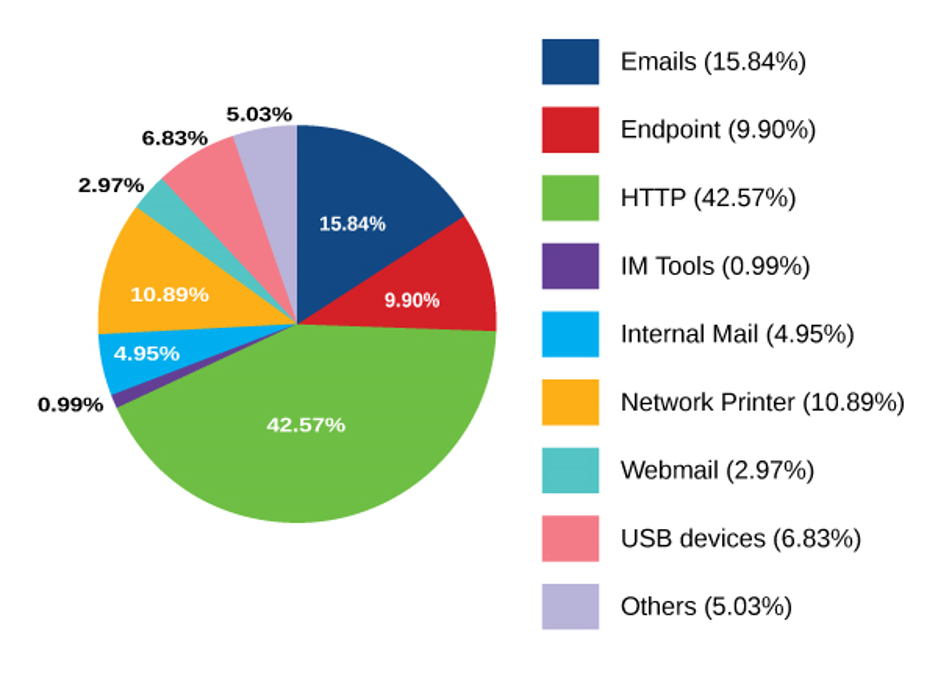
More than 68% of data leak happens through Web and Email and GajShield unique ‘Context Sensitive Data Leak Prevention’ help prevent data leak through these channels.
GajShield’s Data Security Firewall Context based Data Leak Prevention enables to control and mitigate leak of information:
GajShield’s context-based Data Leak Prevention system understands web application/cloud applications by creating context which helps an enterprise to set up policies based on the web application instead of IPs, Usernames which have no relevance to the above application. GajShield firewalls provides visibility to the cloud applications used by an enterprise and also by managing and controlling these applications
GajShield Firewall's Data Leak Prevention and CASB features:
- Detection and Prevention of data leaks
- visibility on the applications used and not just the ports or protocols.
- Monitor and block files being uploaded on the internet with details of the application used and the user who used to upload this file.
- Set policies to monitor/block data leaks via Email, File upload and Chats.
- Set policies to allow read only access to corporate email/social networking.
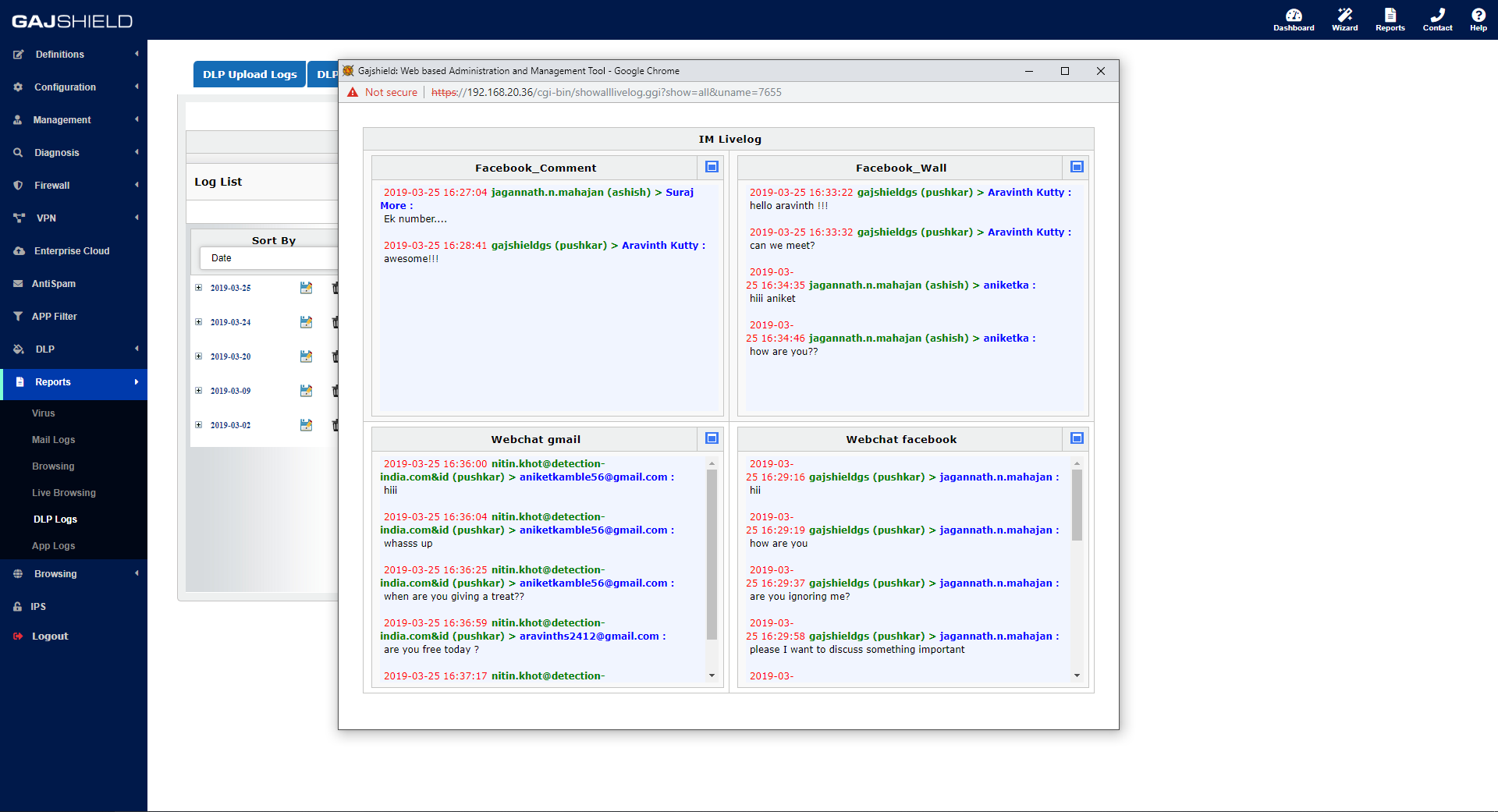
- Monitor IM & Web chats and block content.
- Set policies based on users, groups.
- Set policies based on application context.
- Schedule DLP policies, for example, you may want to allow certain files after a particular time when this information becomes public.
- Get detailed information of outgoing data on internet from your network.
- Detailed Data Upload/Download Logs, File sharing, email and social media logs
- Complete visibility of data going through encrypted HTTPS traffic.
- Powerful DLP Engine sense data on filters set in DLP polices for a granular analysis.
- Economical cost of ownership.
- Monitor & Block unwanted applications like P2P, Open proxies.
- Easy to configure and integrated into single firewall policy window.
- Standard data leak templates provided to quick setup your DLP feature on GajShield firewall.
- Inspects and helps monitor and control applications like G-Suite, Gmail, Yahoo, Rediff, Office 365, Sify, Google Drive, 4shared, Sky drive, one drive, drop box, media fire, box, facebook wall-message-forum post-comment-note-event, WebChat: msn, yahoo, gmail, facebook, IM-chat: yahoo, jabber, msn, gadu-chat and others.
FAQs
Question: Can I block personal email logins and allow only corporate login using DLP in my organization?
Answer: Yes, using GajShield’s DLP, you can set policies wherein a user is allowed only corporate logins and personal login attempts will be blocked
Question: I want to provide just read only access for the web mail where users should not be able to send any mails out. Can DLP do that?
Answer: DLP enables security managers to set policies to allow read only access to corporate emails/social networking.
Question: I want to block all the mails that are not “cc”ed to Head of the department. Can DLP do that?
Answer: You can setup policies based on “From”, “to”, “cc”, “bcc”, subject of gmail and other such Cloud applications. GajShield also provides BYOD (device) and UserSense(user) information.
Question: Can I restrict the file format to allow only document files to be sent?
Answer: Using DLP, one can easily set restrictions on the type of file that should be allowed to be sent. If any restricted file is sent, a notification is sent to the administrator with complete visibility of the file being sent.
Question: Can I monitor my employees Facebook chats and comments?
Answer: Not just Facebook chats or comments but DLP also provides a global visibility through comprehensive and flexible reporting.
Question: Can I set a limit on the size of attachments that are sent out from my network?
Answer: Yes, DLP does very much allow you to set a cap on the size of attachments that are attached or are been sent out.
Question: Does GajShield DLP inspect SSL traffic for Web and Email traffic?
Answer: Yes, GajShield inspects the SSL traffic for both Web and Email (SMTP SSL/TLS & STARTTLS)
Question: Can GajShield DLP block file uploads to DropBox/GDrive?
Answer: Yes, using policies, GajShield’s DLP can effectively block file uploads to DropBox/GDrive and other such applications.
GajShield SOLUTIONS
Centralized Management SystemThe GajShield Sangam is a Centralized Management System dedicated to manage GajShield’s Data Security Firewall all at one place. Sangam enables network admin to manage distributed network of GajShield Data Security Firewalls, managing all aspects of device configuration, push data security policies, global security policies, view all firewall traffic, and generate reports — all from one central location using a single console.
Single Platform for Security.
GajShield Sangam provides administrators of simple or complex network environments with a powerful, intuitive interface to centrally manage multiple GajShield Data Security Firewall appliances including network policies, URL filtering, Data Leak Prevention, Application Filtering, IPS, Gateway Antivirus, Gateway Anti-spam, ISP Failover & Load Balancing and software updates.

One Point Reporting:
Sangam offers Real-time visibility of threat summary and trends. its powerful reporting allows network and security manager to manage and view complete security report from a single management platform.
Centralized Management:
Sangam offers a unified platform for managing all the firewall in the organization’s network. It offer the Ability to individually configure advanced options of the firewall, Ability to define Firewall, IPS, URL Filtering, DLP, Application Filtering, Gateway Antivirus, Gateway Anti-spam, ISP Failover & Load-balancing policy implementation from central offices, functionality to add Groups and configure multiple firewalls together at the same time, feature to retrieve all the firewalls health status in a single dashboard, Intuitive and comfortable UI, ability to work with Pseudo Interfaces/Hosts/User Groups and be independent from firewall constraints like IP addresses and usernames, functionality to take firewall backups and save them in a central location, Add new firewalls to a group to make it act as the one amongst the group, Have the server auto-synchronize all the firewalls at regular intervals, etc.
Single-Touch Deployment:
Single-Touch Deployment. GajShield’s simplified deployment capabilities allow enterprises to ship unconfigured GajShield NGFW appliances to each remote site. When plugged in, the appliance connects to the service in Centralized Management Service Server. Within seconds, the server authenticates the remote device and connects it to a Central Management System for easy policy deployment.
Advantages
- Centralized Policy management
- Easy operations with minimum learning curve
- Flexible deployment
- Consolidated Network and threat visibility
- Reduced operational cost
- Allows grouping of security appliances
- Create policy templates, which can be re-used.
Page 3 of 18
