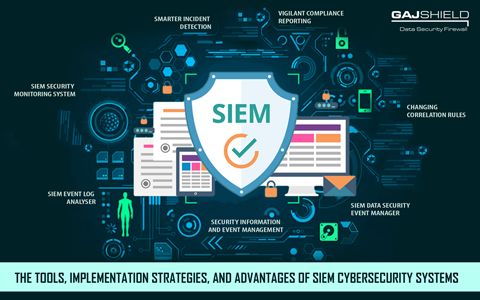
The tools, implementation strategies, and advantages of SIEM cybersecurity systems
Security Information and Event Management (SIEM) is a cybersecurity tool that includes multiple systems and services to provide foolproof cyber-protection for an organisation's data networks. SIEM systems are reliable because they use a holistic approach to deal with data security issues in an organisation. An SIEM system's all-encompassing way of providing cybersecurity helps with safeguarding the organisation's confidential and sensitive information more effectively.
SIEM systems maximise data security by bringing together two different components. Firstly, Security Information Management systems (SIMs) gather data from company records to analyse and create detailed reports regarding known and encountered cyber threats. Information management is important to deal with cyber threats faced previously by organisations. Secondly, Security Event Management systems (SEMs) conduct real-time monitoring of an organisation's data network and the devices connected to it. An SEM relays information to network administrators and data security personnel about vital issues while also establishing correlations between separate security incidents.
SIEM systems provide high real-time transparency for an organisation across its data security infrastructure. Additionally, the collection of data from numerous sources is key for detecting and reporting network threats in a structured way. Generally, SIEM systems provide all their information and network security notifications on an interactive dashboard.
Implementation strategies to exploit SIEM’s core strengths
As a matter of fact, any data security tool is only as good as the implementation practices used by organisations deploying them. Organisations need to implement certain practices and strategies during the incorporation of SIEM systems to maximise their effectiveness. These actions may depend on various factors, such as type of organisation, types of operations carried out, the amount of data flow involved in those operations, specific network security requirements, and others. Some of the best practices in SIEM implementation are listed below:
a) Changing correlation rules
SIEM systems may need a minor tweaking of their in-built, pre-configured correlation rules to identify data security threats that would never be detected in isolation. Isolated threats are generally uncomplicated and can be dealt with by using standard cybersecurity tools. On the other hand, a combination of multiple threats may be hard to detect and cause greater damage to an organisation if not handled early. So, the tweaking of an SIEM system’s correlation rules can be useful to alert network administrators about certain actions or combinations of actions (Example: a combination of five failed logins from an IP address within a certain time-frame followed by a successful login) that may lead to a cyber-attack on the company network. Such a pre-emptive move helps to reduce future attacks. Organisations can create their own rules for specific circumstances too.
b) Identifying compliance necessities
Compliance with regulations is an inherent part of any organisation. Regulations such as GDPR are in place to ensure data security and privacy vigilance on the end of organisations. While scanning through the data security market to purchase an SIEM system, organisations need to clearly assess the data privacy regulations in their country, state or city to be able to purchase wisely. One of the key strategies before SIEM implementation is the careful assessment of data regulations applicable for a given area. Several service providers and software vendors can customise your SIEM system to suit your compliance needs.
On top of that, the purchase decision will also depend on the auditing requirements related to collection of user data, the amount of data retained and stored in the company records, the format of storage, and other aspects before using SIEM for data security of your organisation.
SIEM tools used to prevent cyber-attacks
Here are some of the tools available in the market that can be used for the early detection and prevention of cyber-attacks in organisations. These tools are easily available and are amongst the best SIEM systems for advanced cyber-protection of your data.
● SIEM security monitoring system
Generally, these systems are used for extensive and proactive cloud network monitoring and database management. They perform real-time network monitoring and record management for effective handling of cyber threats.
● SIEM data security event manager
Used for streamlining the process of recording and usage of network security incidents or ‘events’, and to provide a wide range of log management features.
● SIEM event log analyser
Performs tasks similar to an event manager. This SIEM tool helps to manage, safeguard, and mine log files for various types of devices and operating systems.
Advantages of SIEM systems
SIEM is an incredibly proactive data security solution that is used to manage information storage of past network threats and detection of newer ones. Here are a few positive influences that an SIEM system can have on your existing cyber-protection infrastructure:
Smarter incident detection
Most data security tools may not provide the feature of in-built incident detection for users. Such systems, as a result, cannot detect future threats with the same efficiency and regularity as an SIEM system. SIEM tools correlate and evaluate the information stored in their logs to get a whiff of cyber threats that would have been completely overlooked if certain occurrences or combination of incidents leading up to a cyber-attack were not recorded and addressed immediately.
Today’s data threats and breach attacks are highly sophisticated and resilient. So, organisations must implement measures to proactively deal with them or risk running into problems if a competently-orchestrated cyber-attack is allowed to permeate their data network and affect their devices and storage facilities.
And finally, if a threat is too great and even an SIEM system cannot stop it, the data security tool can at least mitigate the damage caused by it.
Vigilant compliance reporting
SIEM systems make it easier for organisations to adhere to data privacy regulations by simplifying the process of periodic compliance reporting. SIEM tools provide centralised data logging provisions to make the process more systematic. SIEM systems negate the need for network administrators to manually fetch data from each host in an IT environment. Without an SIEM system, they would have to painstakingly assemble single reports from such kinds of data. Retrieving data from various hosts is time-consuming as each host may have different log-in protocols. Ultimately, the process correlation becomes challenging if an SIEM system does not collect and collate the data.
As we have seen, SIEM provides next-level data security with optimal compliance reporting. Organisations around the world must implement these systems to reduce their chances of being on the wrong end of cyber-attacks. Gajshield’s data security experts can provide valuable advice regarding the ways in which your organisation can strengthen its cyber-protection foundations. Apart from SIEM, Gajshield offers a host of products and services that will bolster your existing cyber-protection infrastructure. Please contact us to discover more about our products and services.
Get In Touch With Us
Subscribe to our Newsletter
2026 © GajShield Infotech (I) Pvt. Ltd. All rights reserved.
